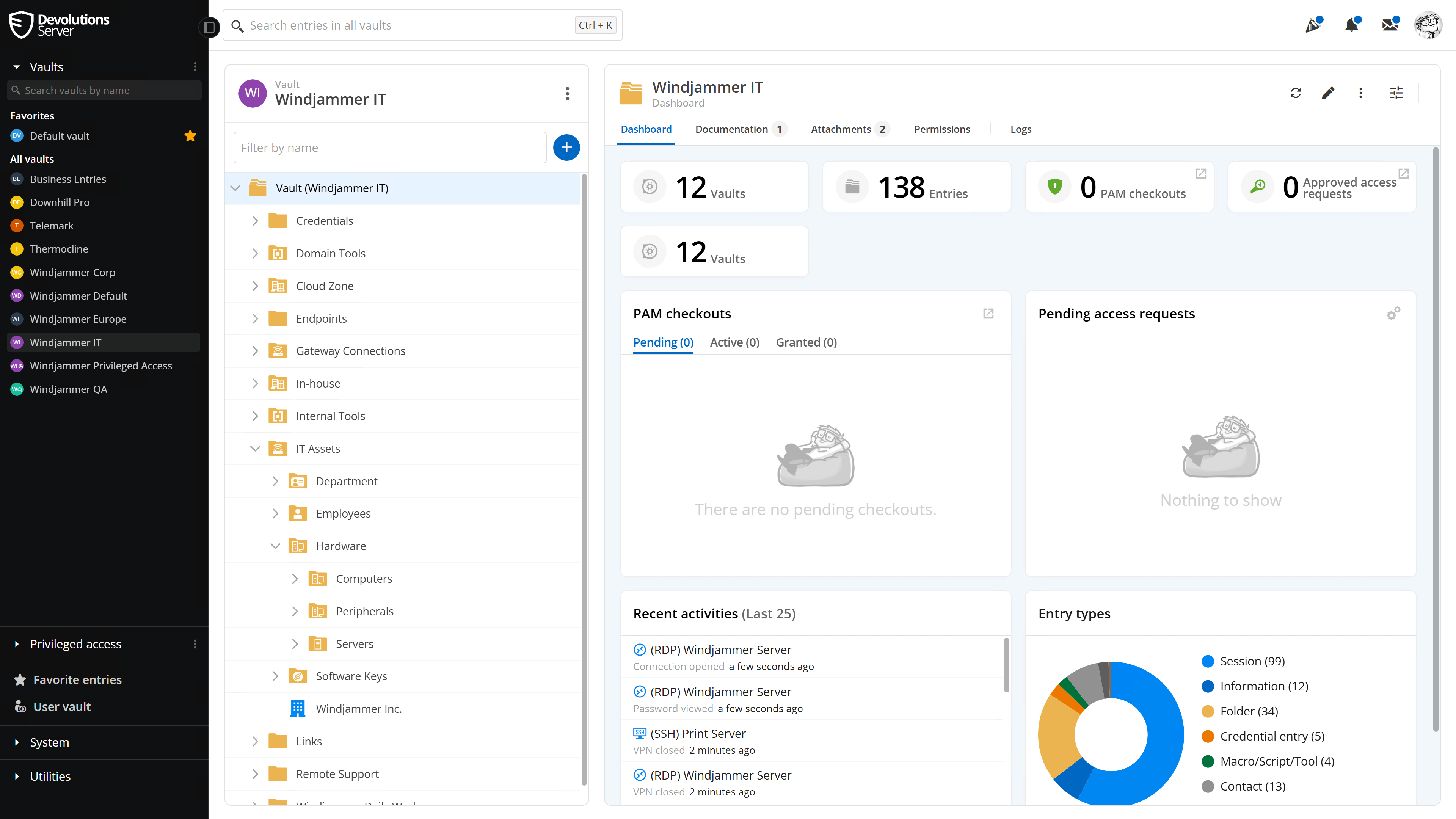
Privileged access management
Experience IT-led PAM: deploy fast, stay in control, and meet compliance without the enterprise cost.
Privileged access management
For SMBs and mid-market organizations that need real PAM outcomes without months of rollout. Deploy quickly, keep control in IT, and prove compliance from day one, all without adding administrative overhead.
Included
From foundation to governance - Everything you need, built-in
Vaulting & Discovery

Control & Automation

Advanced protection
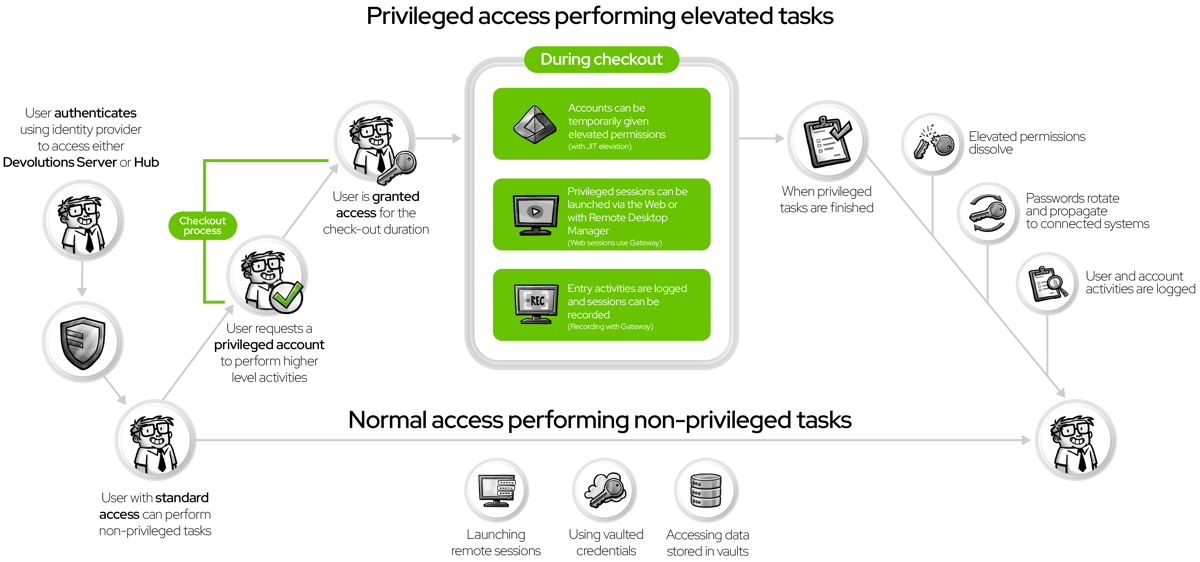
Enforce least privilege and eliminate standing access.
- Just-in-time provisioning & elevation - assign privileges only when needed
- Delegate temporary access with automatic revocation
- Enforce zero standing privilege and least-privilege principles
Ongoing improvement
Drive accountability and strengthen security posture.
- Centralize audit logs and reporting for ongoing visibility
- Extend governance through REST API and integrations
- Detect anomalous activity and track progress toward security goals
Understanding the privileged access workflow

Replace MIM (Microsoft Identity Management) with Devolutions privileged access management
Do you need to broker access to on-premise Active Directory accounts, but is the thought of deploying Microsoft Identity Management (MIM) daunting?
Deploying on-premise MIM is a complicated and challenging process. Instead of trying to navigate a complex web of documents and configurations, the Devolutions Privileged Access Management add-on to Devolutions Server offers a robust and flexible approach to brokered account access.
Discover how to manage account checkouts, automatically reset passwords, and import new managed accounts easily with Devolutions Privileged Access Management!

Replace Entra ID PIM (Privileged Identity Management) with Devolutions privileged access management
Despite your organization moving to Entra ID, does the Privileged Identity Management (PIM) solution licensing appear out-of-reach or not user-friendly enough?
The Devolutions Privileged Access Management (PAM) add-on to Devolutions Server offers uncomplicated licensing with a modern web interface. Perfect for remote workers who need brokered account access, PAM flexibility extends to integration with custom account data sources to support every tool you have.
With easy managed account checkouts, automatic password resets, and easily imported accounts take your account management to the next level with Devolutions Privileged Access Management!

Integrate Devolutions privileged access management with Remote Desktop Manager
Does your organization already use Remote Desktop Manager (RDM) but wants to further secure and manage account access?
With deep integration to RDM, add Devolutions Privileged Access Management (PAM) to Devolutions Server and empower your users to check out passwords knowing that upon completion, the accounts will automatically rotate their passwords, ensuring safety on subsequent access.
In-depth auditing and managed account access has never been easier with the Devolutions Privileged Access Management add-on to Devolutions Server!
Complete PAM, compact price
Smaller team? The Starter Pack gives you full PAM coverage for up to 5 users — with the same features, at half the cost.

Resources
Learn more about our solutions by checking out our curated resources and see how privileged access management can help improve security within your organization!