Packages
management & IT operations
Boost productivity, decrease costs, and increase security with a centralized platform where you can manage a wide range of remote connections and tools.
Improve your security strategy without reducing productivity by using a password management solution.
management
Diminish the risk of insider threats and cyberattacks while providing audit and compliance requirements for your team.
management
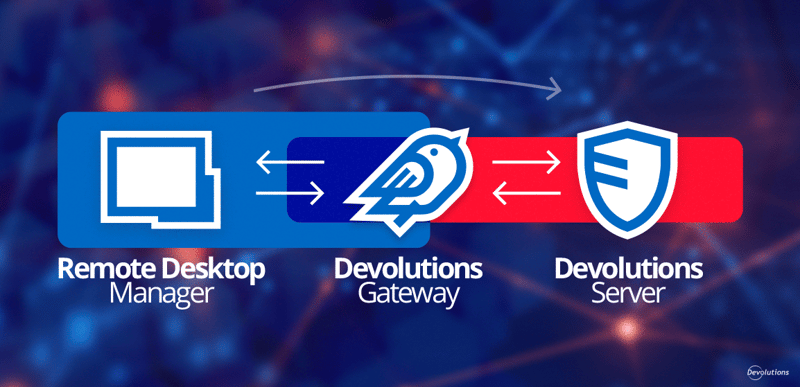
Establish a secure entry point for internal or external segmented networks that require authorized just-in-time (JIT) access.
Streamline routine IT tasks and boost productivity with integrated scripting, orchestration, and reporting.
Remote Desktop Manager Free
Best all-in-one remote connection and credential management tool for independent IT users
The whole power of Devolutions half price for teams of 5
Quick overview
Your trusted partner in security and compliance.
Unified solutions: seamless integrations with Devolutions
Remote Desktop Manager
The best remote connection manager in the industry
Improve your security strategy without reducing productivity by using a password management solution.
Discover, install, and update all your Windows packages
Automate remote management with dashboards and APIs
Secure, rotate, and audit every privileged account across your infrastructure
Your FREE go-to hub for mastering Devolutions' suite of products and services.
The Devolutions Forum is the place to go to connect with your peers and the Devolutions team.
Get answers to product specifications, settings and more on our documentation.
Stay up to date with our weekly articles on our blog, the toolbox for your IT success.